The other day, Federico asked about why people use web services such as IFTTT. I have a few of these that I use frequently, but the geekiest one is this: controlling my Mac with my car.
More specifically, when I turn my car’s ignition on or off in the parking lot at my office, Automatic triggers an IFTTT recipe, creating a text file in a special Dropbox folder which is monitored by launchd and runs a shell script depending on which file is created.
It sounds more complicated than it is. No, really.
What can these shell scripts do?
There are many possibilities for what these scripts can do, but here are some examples of what I do.
When my ignition turns on
When my ignition turns on, that means that I am leaving my office, which could mean for lunch (I’ll be back in an hour), an off-site meeting (I’ll be back in an hour or two), or it’s the end of the day (I’ll be back tomorrow or the next business day).
When my ignition turns off
When my ignition turns off , that means that I am arriving at work.
If you use network drives, this would be a good time to (re)connect to them. You could also launch iTunes or Spotify if you listen to music at work. Basically anything that you normally wait for your computer to do when you first arrive at the office, you can get started before you even walk in the door.
“Ok… how?”
Now that you hopefully understand the big picture overview, I’ll get into the specifics of how to put this together.
- You need a car with an Automatic device.
- You need accounts with IFTTT and Dropbox.
- Create a folder in Dropbox. This can be any folder, but I will be using /Users/jsmyth/Dropbox/IFTTT/Automatic/IgnitionAtWork/ in my examples.
- A
launchd plist in ~/Library/LaunchAgents/ which monitors the folder from step #3.
- A shell script to run from the
launchd plist. This can be called anything you want, but I will be using /usr/local/bin/IgnitionAtWork.sh in my examples.
- Two geofenced triggers in the iOS IFTTT app: one which creates an “IgnitionOn.txt” file and one which creates an “IgnitionOff.txt" file.
Example launchd plist
Here is an example launchd plist.
- Change the
Program key to be the name of the shell script
- Change the
QueueDirectories key to point to the directory that you created.
Note that you cannot use ~ or $HOME to refer to your home directory in a launchd plist, you must provide the full, exact path.
<?xml version="1.0" encoding="UTF-8"?>
<!DOCTYPE plist PUBLIC "-//Apple//DTD PLIST 1.0//EN" "http://www.apple.com/DTDs/PropertyList-1.0.dtd">
<plist version="1.0">
<dict>
<key>Label</key>
<string>com.tjluoma.IgnitionAtWork</string>
<key>Program</key>
<string>/usr/local/bin/IgnitionAtWork.sh</string>
<key>QueueDirectories</key>
<array>
<string>/Users/jsmyth/Dropbox/IFTTT/Automatic/IgnitionAtWork/</string>
</array>
<key>RunAtLoad</key>
<false/>
</dict>
</plist>
(Note: this is available as a GitHub gist).
Save it to ~/Library/LaunchAgents/com.tjluoma.IgnitionAtWork.plist
Example shell script
The contents of IgnitionAtWork.sh are really up to you. This is just an example to show how you might put it together.
#!/bin/zsh -f
# Important! DIR _must_ be the same as whatever directory you used
# for `QueueDirectories` in the `com.tjluoma.IgnitionAtWork.plist`
DIR="/Users/jsmyth/Dropbox/IFTTT/Automatic/IgnitionAtWork/"
# if the directory does not exist, exit
cd "$DIR" || exit 0
# get rid of this file, which will cause `launchd` to keep triggering
rm -f .DS_Store
command ls -1 \
| egrep 'IgnitionOn|IgnitionOff' \
| while read line
do
case "$line" in
IgnitionOn*)
###########################################################################
## BEGIN OPTIONAL SECTION for when Ignition is turned on
## Change this in this section to suit your needs
# run BitTorrent Sync application
open -a 'BitTorrent Sync'
# mount TimeMachine drive, if not mounted
[[ ! -d '/Volumes/TimeMachine' ]] && diskutil mount TimeMachine
if (( $+commands[lock.sh] ))
then
# if the 'lock.sh' script is found, run it
lock.sh
else
# otherwise, just lock screen by switching to login window
'/System/Library/CoreServices/Menu Extras/User.menu/Contents/Resources/CGSession' -suspend
fi
## END OPTIONAL SECTION for when Ignition is turned on
###########################################################################
# This deletes the file so that launchd doesn't just keep triggering the script
rm -f "$line"
;;
IgnitionOff*)
###########################################################################
## BEGIN OPTIONAL SECTION for when Ignition is turned off
## Change this in this section to suit your needs
# launch apps that you want to have run when you get to the office
# these are just some examples
open -g -a 'OmniFocus'
open -g -a 'BusyCal'
open -g -a 'MailMate'
## END OPTIONAL SECTION for when Ignition is turned off
###########################################################################
# This deletes the file so that launchd doesn't just keep triggering the script
rm -f "$line"
;;
esac
done
exit 0
# End of shell script
(This shell script is also available as a GitHub gist.)
Example IFTTT recipes on iOS
Step 1) Create IFTTT recipe for when the ignition turns ON in a specific area
When you launch the IFTTT iOS app, choose “Automatic” and then “Ignition turned on in an area” as the “Trigger”:
Note: If you are not in the area that you want to use as the trigger, you can manually select the area that you want to use, but it is easier to do this when you are already at the area that you want to use as the IFTTT trigger. For example, since I wanted the geofence to be the parking lot at my office, I waited until I was there before creating the IFTTT recipes.
Next, choose “Dropbox” and “Create a text file” as the “Select Action”:
This part can be a little confusing. When you first create the IFTTT recipe, it automatically chooses the folder (IFTTT/Automatic) and the filename for you. You have to select the recipe and tap “Edit”
then scroll down to change the filename and folder:
Step 2) Create IFTTT recipe for when the ignition turns OFF in a specific area
Once you have completed Step 1, repeat the process except when you launch the IFTTT iOS app, choose “Automatic” and then “Ignition turned off in an area” as the “Trigger” instead of “Ignition turned on in an area.”
There are a few provisos, a couple of quid pro quos…
This system is not foolproof.
Occasionally I realize that the IFTTT action failed to run for some reason. Launching the IFTTT app on my iPhone usually fixes this. The IFTTT iOS app can send you a push notification when recipes run, which is a good idea so that you know it is working. If Dropbox is not running, or if it is busy doing something else (like reindexing itself for the millionth time, not that I’m bitter), it might not sync the IFTTT file right away.
There have been times when I have been at the office for an hour and then suddenly Dropbox says “Oh, wait, here’s that file” and then launchd runs the “Oh, you have just arrived at the office!” script.
A few times I have been sitting at my desk after being at my office for a long time when suddenly I received an IFTTT notification that the ignition in my car had just started. It was a little disconcerting the first time it happened, but now whenever I notice that something isn’t working properly I just launch the Automatic and IFTTT apps on my iPhone, and that seems to solve the problem. (I assume these issues are caused when the iPhone runs out of RAM and kills off background processes, but that’s just a guess.)







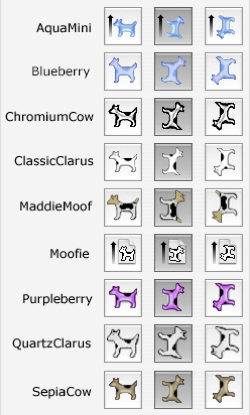 Recently, Apple marked a major Mac anniversary. Celebrate the next 30 years of Macintosh by ditching this guy and replace him with a classic Clarus in your print dialog. Roby Sherman's ClarusX2014 offers a full
Recently, Apple marked a major Mac anniversary. Celebrate the next 30 years of Macintosh by ditching this guy and replace him with a classic Clarus in your print dialog. Roby Sherman's ClarusX2014 offers a full 




